{{item.title}}
{{item.text}}

{{item.text}}
How to protect against disruptions and data losses

Today’s cybersecurity challenges are unlike any we’ve experienced before. The guiding principles have shifted. The rules of the game are no longer obvious. Today’s challenges require more than the expected—seeing beyond today to manage the risks and disruptions of tomorrow.
That’s why we deliver an innovative combination of human ingenuity and technologies to assess the global threat landscape. Our professionals—powered by technology—are committed to helping you protect everyone, and everything, you care about. We're here to get you future ready.
As your company develops its threat intelligence maturity, we’re here to help. We work with our clients and partners as a community of solvers, generating trust and delivering results along every step of your journey: supporting in-house threat intelligence capabilities; building new data feeds; collecting, analysing, and distributing timely details on potential attacks; providing global visibility on the threat landscape. So you can better understand your risk profile, make informed decisions and mitigate new threats.
Get timely, tactical, and strategic data on the global threat landscape. So you can make more informed, risk-based decisions.
Threat intelligence reporting
Stay ahead of the game with technical reports on new targeted attack campaigns, as well as strategic reporting on a particular region, sector, or actor of interest to your organisation.
Threat intelligence data
Monitor ongoing threats with a high-confidence feed of single value indicators associated with targeted attacks. Access network IDS and file detection signatures. Contextualise relationships between indicators and threat actors. Formats supported include network detection (via Suricata or Snort) and end point detection content (via SIGMA or Yara).
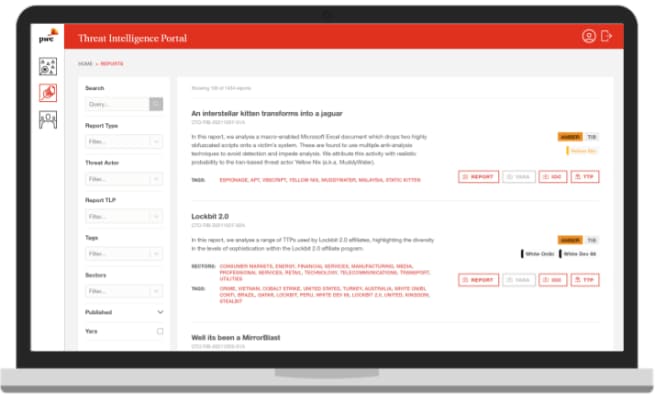
Threat intelligence portal
Use this site as a resource to access the most relevant threat research to your organisation, including our reporting, technical data, and threat actor information. Query threat data, including indicators of compromise, and tailor feeds to your areas of interest.
Threat context
Access a private collaboration space, with direct access to our analysts, providing broader context around the threats you’re investigating. People and technology work hand in hand to deliver faster, more intelligent and better outcomes.
Gain insights from continuous, customised research that can include monitoring of dark web forums, social media platforms, and corporate digital estates, as well as executive profiling and keyword searches to determine credential leakages and potential domain infringements.
Empower your teams with bespoke reports and personalised support from our analysts on the specific threat actors, campaigns, malware, and malicious indicators of most interest to your organisation.
Enhance your ability to consume, apply or produce intelligence with a maturity assessment, threat intelligence programme development, and threat modelling. We deliver quality through integrity, unwavering objectivity, and heavy investment in data, tools, tech, products, and services.
{{item.text}}

{{item.text}}

Cyber Threat Operations Lead Partner, PwC United Kingdom
Tel: +44 (0)7725 707360