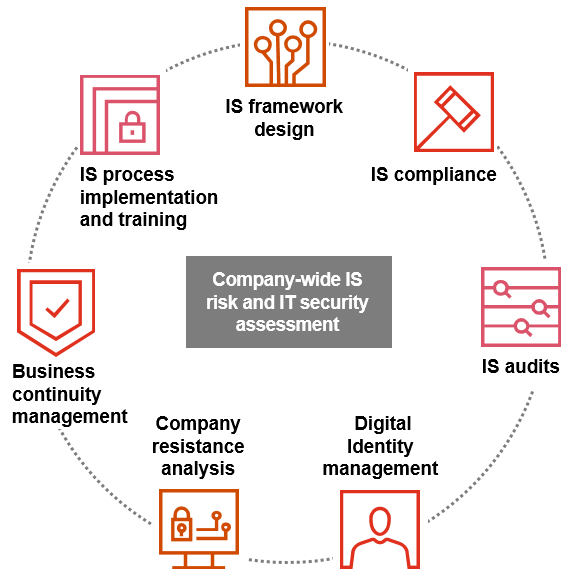
A cybersecurity assessment is a comprehensive review of your organization’s security posture. It evaluates policies, processes, technologies, and controls to identify gaps and measure maturity against industry standards. This usually includes risk identification and prioritization, governance and compliance checks, security architecture reviews and recommendations for strategic improvements. It’s typically non-intrusive, focused on prevention and resilience, and is ideal for organizations seeking to align security with business goals. Use cybersecurity assessments to understand your overall security maturity and compliance readiness.
Penetration testing (or ethical hacking) is a simulated cyberattack designed to uncover exploitable vulnerabilities in your systems, applications, or networks. It goes beyond surface-level scanning by actively exploiting weaknesses, demonstrating real-world attack scenarios and providing detailed risk analysis with remediation guidance. Pentesting is natively offensive and threat-focused, often performed periodically or after major system changes. Use penetration testing to validate your defenses and uncover critical vulnerabilities that attackers could exploit.