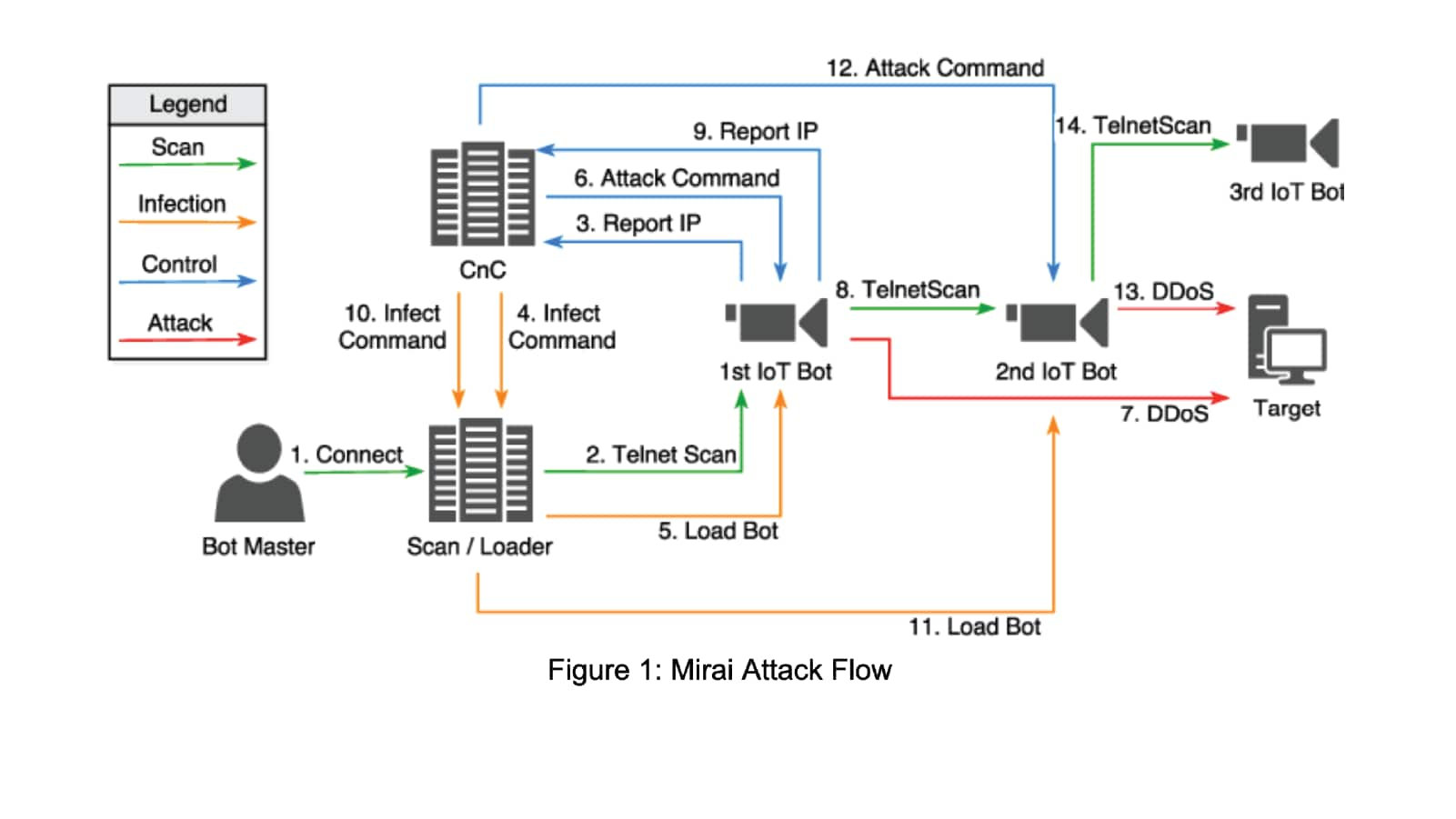
Attackers often target Internet of Things (IoT) devices, which typically have weak security. For instance, they deploy malware to enrol victims into the Mirai botnet to turn these devices into tools for DDoS attacks, leveraging their often inadequate security configurations.
Malware is deployed to enrol victims’ devices into botnets like Mirai to be used for DDoS attacks