The role of digital trust in today’s accelerated digital landscape is more pronounced than ever before. Security leaders are working closely with business teams to strengthen organisational resilience. There is a more integrated approach to digital and data security with new layers of protection due to real-time risk monitoring systems. As a result, cyber is leveling the playing field with attackers, pushing back and fending off attackers like never before.
Today, a digital-first strategy is key to pivoting back to a steady growth path and securing the future of businesses in the new world. Digital trust is undoubtedly integral to the digital-first strategy.
For a digital-first strategy, what are the considerations keeping Chief Information Security Officers (CISOs) awake at night?
- In a post-COVID-19 world, is your defence ready?
- Establishing risk compliance
- Staying ahead of new trends and competitors
- Instilling confidence in stakeholders
In a post-COVID-19 world, is your defence ready?
The best defence is often offense. If organisations are able to threat-hunt effectively and find cyber attackers before they strike, the battle is half won.
Establishing risk compliance
Keeping government regulations in mind is key for organisations to holistically embed cybersecurity into every major business decision. The Singapore Personal Data Protection Commission (PDPC) is updating the Personal Data Protection Act to increase the responsibility of organisations in the event of data loss - via mandatory reporting and increased penalty. This brings cyber regulations to the forefront, with an increased need to invest in capabilities processes and technologies to prioritise these considerations in all business decisions.
Staying ahead of new trends and competitors
With new cyber crimes constantly discovered and reported in the news - especially when attackers have the opportunity to get creative due to remote working (new phishing emails, social engineering attacks, hidden malware and more) with newer and more sophisticated attacks - businesses need to be ready to respond to a wide range of threats ranging from nation states and organised crime, to ‘hacktivists’ and insiders.
Instilling confidence in stakeholders
Post COVID-19, CISOs are likely to be involved in business decisions more than ever. To instill confidence in stakeholders, the key is to ensure that the cybersecurity function is delivering value and contributing to your firm’s overall business goals.
Turn challenges into opportunities: open new doors in Digital Trust

1. Cloud trust
With a transition to remote ways of working, we empower organisations to lean on public cloud services for greater efficiency at a lower cost. The future of cloud is now.
Learn more
2. Digital Identity
We can help to connect the right people to the right data and systems, tailored to their individual access levels and needs through user assessment. This includes identity lifecycle management and governance, consumer identity and access management and privileged access management.
Learn more
3. Cyber strategy and management
With cybersecurity growing as a business imperative, we can come in to help develop or re-design cybersecurity due diligence and strategies as well as target operating models.
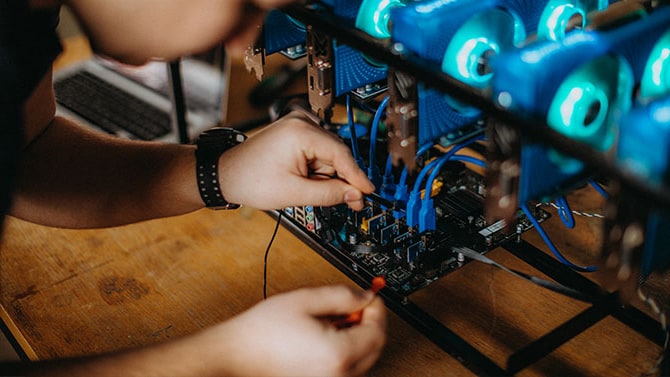
4. Cyber defence
Building a resilient cyber defence as well as a defined response framework are crucial to ensuring a company's ability to minimize damage and recover rapidly in the event of a cyber attacks. Our professionals can assist with vulnerability management and threat intelligence, security monitoring and analytics, security incident and threat management, and SOC automation and orchestration, so you can confidently prepare, identify, respond, investigate and remediate threats.Learn more


5. Cyber threat intelligence
Trusted threat intelligence can help to provide timely, actionable intelligence to understand the emerging threats, stay on guard and always be one step ahead of cyber attackers at every stage.
6. Data privacy and protection
Personal data usage and cross-border data transfers are now a part of everyday business transactions in the digital age. Embedding the right security protocols such as data classification, discovery and loss protection, enterprise, network and cloud data protection and personal data privacy, can help to establish trust in the powerful world of data.
7. Operational technology
The increasing integration of information technology and operational technology systems open new doors - we can help with assessments, compliance and training and education.
PwC’s Cybersecurity Alliances

Awards
- PwC named as Asia Pacific Japan Delivery Admiral Partner of the Year 2025
- PwC named as Asia Pacific Japan Advisory Partner of the Year 2025
- PwC named as SailPoint Asia Pacific Japan Solutions and Advisory Partner of the Year 2024
- PwC awarded the SailPoint Delivery Admiral Asia Pacific Japan 2024 Award
Contact us





